Disclaimer: the story about Rita the Designer and Johnny the Hunter is fiction. The filesilo hack is not.
Rita designer was working on a new project and was on a deadline. She was an avid reader of the magazine “Web Designer“, that has lots of great content on UX and design patterns. Usually Rita wouldn’t base her client designs on stuff from a magazine but this time she found some really nice UX effects described in the latest issue that she wanted to try out. She created an account on their fileshare “FileSilo“, and quickly found the free stuff she could download when she’d bought the latest Web Designer issue. When she signed up she used her e-mail address and the password she always used for her non-critical online accounts, which in her opinion was pretty much anything except for her banking portal and her insurance portal.

Rita downloaded the content, opened the zip file and looked through the templates; all good. She then decided to have a latte at the nearest coffee shop while thinking about the exact transitions she wanted to build into the site. In the coffee shop, she stumbled across a friend from university, who was now a security researcher with a anti-malware company. They started talking about their latest gossip. The sec researcher, Johnny the Hunter, told her he had a new girlfriend he’d met on tinder, and that work was a bit slow now. He’d recently gotten a contract with a publishing house to help with securing their web infrastructure but he hadn’t yet started. Rita told him excitedly about the new UX transitions she’d found in Web Designer, and that she had downloaded the templates from filesilo, ready to implement. The customer was expecting the first conceptual design by end of the week, so she expected to spend a lot of time working this week.
She got back to her studio office and started playing with the transitions; it looked very good, and she was impressed with the usability of the templates without much fudging around. On Friday, she met with the client and showed him 3 different implementations – and they were equally impressed with all, finally selecting her green design with a flip effect for their new landing page.
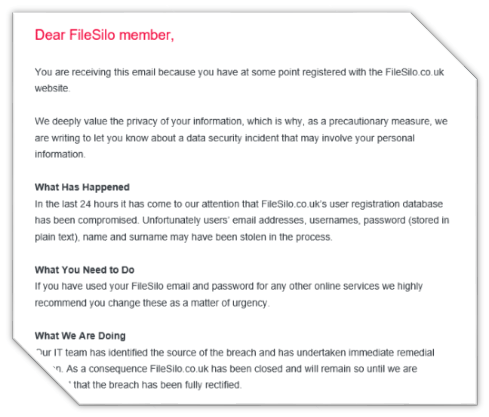
Rita went back to the coffee shop to celebrate and get ready for the weekend after having worked like a maniac all week to get the design concepts done. She looked at her phone, and discovered she had two new emails. The first one was from the guy she’d met earler in the week, Johnny the hunter, urging her to check her online accounts and make sure she hadn’t reused any passwords in the filesilo site – because it had been hacked. So what, was her first thought, passwords are stored in encrypted form anyway? The other email was from the Future(!?). Stating that the passwords were stored in clear text at filesilo, that they were sorry and that she should go ahead and secure her online accounts.
OK, at least it is good that they are telling people about the breach at once so I can secure my other accounts, she thought to herself. She should really stop using the same password everywhere. Then she got a text – somebody has logged into her Facebook account. From Kinshasa. Not good. Same password. Another text. From Microsoft: her onedrive is being accessed. From Taiwan. Worse. Ok, time to panic!
How could this happen?
Obviously filesilo had a very shoddy operation going, storing passwords in plain text. The Register has a story on this, with a very fitting photo to illustrate the case. And how could it happen? Complacency, lack of awareness, stupidity? It is very hard to get a grasp on, especially from a magazine in the IT sector! Obviously filesilo just did unfathomably stupid things in designing their downloads page but another question I’m sure Johnny the Hunter would have for Rita the Designer is “why didn’t you notice all the clues”? Like no https. Like accepting weak passwords.
These things happen because knowing what to do isn’t enough – people need to make secure behaviors habits. If not it is going to slip whenever you are in a hurry. This is why one-off awareness programs aren’t that efficient. So, it looks like the publishing house learned some stuff from Johnny the Hunter. In an email sent out today, they say they’ve done the following since the hack:
- The site now uses HTTPS meaning all user data is encrypted as it is sent to our servers
- All site components have been updated to the latest most secure versions and functionality has been added to ensure that future security updates are applied immediately after release
- All passwords are now fully encrypted using an updated secure algorithm
- Minimum requirements for password strength has been added to reduce the risk of successful “brute force” attacks
- ReCaptcha has been added to the registration process to reduce chances of automated hacker/spammer sign ups
- All staff users with access to subscriber data require “two factor authentication” to log in. This further reduces the risk of hacks where user data could be compromised
All good practices that should have been there for years. It probably would have been if they had installed an information security management system, as they are likely to need after the General Data Protection Regulation comes into force in 2018.
