Boards are responsible for the health of the company and its ability to fulfill its mission on behalf of its owners. This is why most boards put a lot of effort into effective risk management with robust processes in place for compliance, financial risks and M&A activities. What they very often fail to do, is to incorporate robust controls for the cybersecurity of their company’s operations. In fact, a study surveying a large number of board directors show that risk and security is the area they feel is most challenging to cope with, yet is also an area where they feel strategic threat is lower than many other threats such as financial or compliance risks. This, in spite of the spikes in cyber attacks hitting businesses globally in 2016, and that the average cost of a data breach has been estimated to about 4 million USD (by IBM). The key to understand both the underestimation of the risk posed by cyber threats, and the lack of good processes to follow up cybersecurity risks as a corporate governance activity, are both linked to the cybersecurity skills gap – that reaches all the way to the senior leadership and board levels.

Getting the cybersecurity processes in place
It is not easy to close the skills gap at any level but one should also not underestimate what can be achived through the use of good practices, eduacting the staff and integrating the approach to risk management into the operations of the company.
Where to find best practices?
Cybersecurity has come a long way, and several standards and practice documents exist, ranging from detailed technical requirements, to management processes. Building an information security management system is no easy undertaking, but using a risk based approach and following the same principles as for other governance structures help. Making ISO 27001 (an international standard) your basis for information security mangement will put you off to a good start. To get a practical how-to on building up such a system, see this post: How to build up your information security management system in accordance with ISO 27001
Metrics and Context: the link between operations and strategy
The board can not head into every aspect of security operations, nor does it (typically) have the expertise to dive into all details. That’s why it is important to develop a robust set of security metrics that can be reported ot the board, making sense of both the threat landscape, the context and the maturity of the company to deter, detect and deny cyberattacks, as well as to recover from those that inevitably will outsmart your defenses. Developing metrics should be done such that it fits with the greater strategic picture, recognizing that cybersecurity also ties into all of the firm’s operations. Viewing the metric game should thus include the financial perspective (most companies focus a lot on this), the customer perspective (tends to be forgotten in security), the learning and innovation perspective (often done only on the tactical level, not linked to strategy) and the internal process perspective (sometimes dominating, sometimes not existing at all).
In addition to developing metrics, boards should also be kept up to date on the risk context: what are our most valuable data assets and IT infrastructures? How is our standing with respect to hacker interest (scripters? hacktivitsts? nation states?). Do we have good people managment in place, and how does our internal corporate life affect the insider threat? It is the responsibility of the CISO to educate the board enough to make them able of both asking these questions and understanding why they are as important as understanding the strategic fit in a M&A transaction.
The compliance link
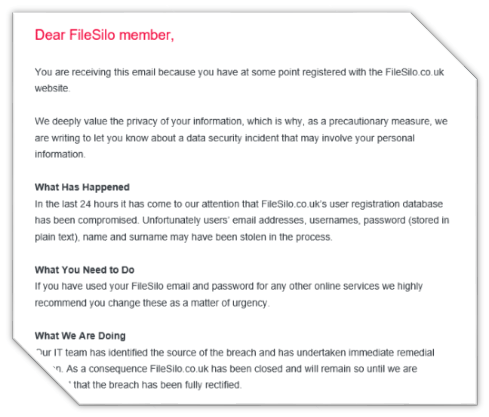
Compliance is already on the table, and cybersecurity regulation is taking shape in different jurisdictions. Mapping out regulatory compliance requirements to cybersecurity, as well as data privacy, is key to ensuring compliance in today’s operating environments. In the EU and EEC area a new regulation is coming into force in 2018 with strict requiremetns to most businesses dealing with customer data – yet few companies are ready to deal with this. Bringing the cybersecurity domain into the compliance picture is a necessary cornerstone of corporate governance, and for strengthening board focus. For an overview of new requirements to businesses from the General Data Protection Regulation (GDPR), see here: What does the GDPR (General Data Protection Regulation) mean for your company’s privacy protection and cybersecurity?
The people factor
Boards are no better than the people setting on it; this is why getting technical competence on boards should be a major priority for stockholders. We are living in the age of digitalization, of machine learning and of cyberthreats: believing that we can deal with this without technical competence also on the top of governance is simply superstition.
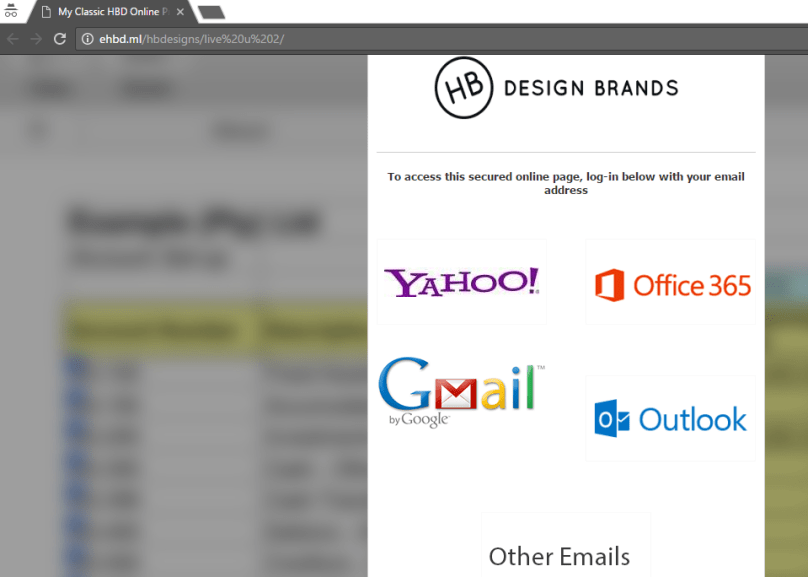
Also, for the processes to work, it is important that everyone has a feel for what secure behaviors are, and what consititues risky behaviors (without rewards). Driving security awareness in the corporate culture is also a key factor for directors, and overseeing this as part of the risk goverannce should be a board priority. Almost every breach starts with a social engineering campaing – getting your people on the right side of the knowledge gap is probably the best investment you can make after turning on your firewalls, autopatching of computers and removing end-user’s admin rights.
To drive awareness in an effective manner, make sure it is suitable for its audience, and that it is noe a one-off e-learning module to click through. Building a security aware culture is a change process, not a simpel training event: When does cybersecurity awareness training actually work?
Take-away points
This are your talking points from this article – bring them to your next board meeting or coffee break at work:
Insider Extra: slide deck with implementation tips for your corporate governance processes.